Problem
When using a Bitbucket Server or Data Center integration with HCP Terraform, you may be unable to update the integration or see VCS-backed modules and repositories populate automatically. Actions that rely on the VCS connection may fail.
Cause
This issue commonly occurs when the Bitbucket instance uses a self-signed SSL certificate. The git client used by HCP Terraform does not trust the certificate provided by the server, resulting in SSL certificate errors that prevent communication.
Solutions
There are two approaches to resolve this issue. The recommended solution is to configure your local Git client to permanently trust the self-signed certificate. A temporary workaround is also available for one-time operations.
Solution 1: Temporarily Disable SSL Verification (Workaround)
For a one-time operation like cloning a repository, you can temporarily disable SSL verification for a single command. This is not a permanent solution.
Execute your git command with the GIT_SSL_NO_VERIFY=true environment variable.
$ GIT_SSL_NO_VERIFY=true git clone https://username@git.example.com/scm/repository.git
Alternatively, you can disable SSL verification globally, but this is not recommended as it poses a security risk.
$ git config --global http.sslVerify false
Solution 2: Configure Git to Trust the Self-Signed Certificate (Recommended)
This two-step process configures your Git client to recognize and trust your Bitbucket instance's certificate, providing a permanent solution.
Step 1: Obtain the Self-Signed Certificate
You can retrieve the certificate from your Bitbucket server using OpenSSL or directly from your web browser.
Option A: Use OpenSSL
Run the following openssl command, replacing NAME and HOST:PORT with your Bitbucket server's details. This command saves the certificate to a file named certificate.pem.
$ echo | openssl s_client -servername NAME -connect HOST:PORT |\ sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > certificate.pem
Option B: Use a Web Browser
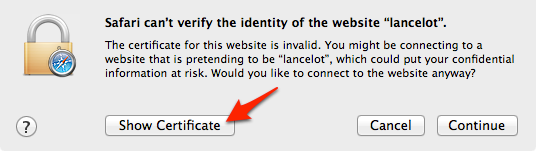
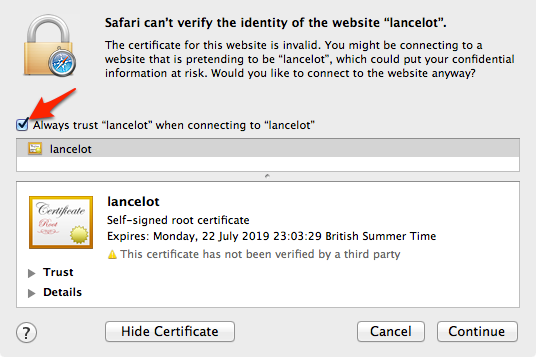
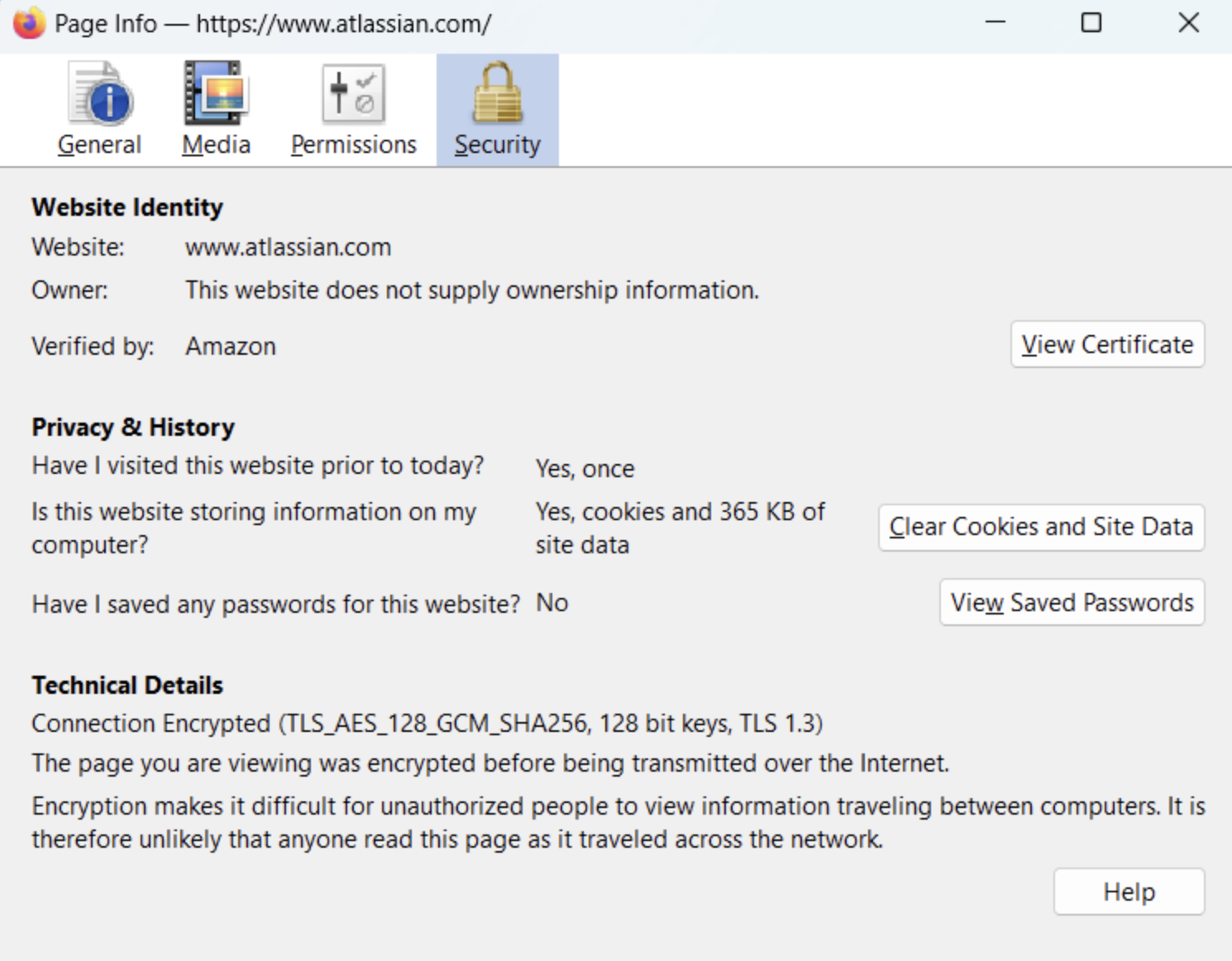
You can also export the certificate directly from your browser. The process varies by browser and operating system.
-
Export Certificate in macOS (via Chrome or Safari): For instructions, see the Atlassian documentation on Resolving SSL self-signed certificate errors.
-
Export Certificate From Firefox: For instructions, see the Atlassian documentation on Resolving SSL self-signed certificate errors.



Step 2: Configure Git to Trust the Certificate
Once you have saved the certificate file, instruct your Git client to use it for SSL validation.
-
To use the certificate during the initial clone, set the
GIT_SSL_CAINFOenvironment variable.$ GIT_SSL_CAINFO=/path/to/certificate.pem \ git clone https://username@git.example.com/scm/repository.git
-
To ensure all future interactions with this repository also work, navigate into the repository directory and configure the local Git settings.
$ cd repository $ git config http.sslCAInfo /path/to/certificate.pem
Additional Information
Note that Atlassian's support for Server products ended on February 15, 2024. If you are running a Bitbucket Server product, refer to the Atlassian Server end of support announcement to review your migration options.
