Introduction :
Many customer raised the ticket for giving access to user for a particular keys inside the KV secret engine. Generally people make mistake in creating a policy for accessing keys inside KV secret engine. So in this article we will define how to write the policy to access the keys inside KV secret.
Steps to enable kv secret engine:
vault secrets enable -path=kvV2 -version=2 kv
vault kv put kvV2/env/qa/account name=account
vault kv put kvV2/env/dev/account name=account
vault kv put kvV2/env/prod/account name=account
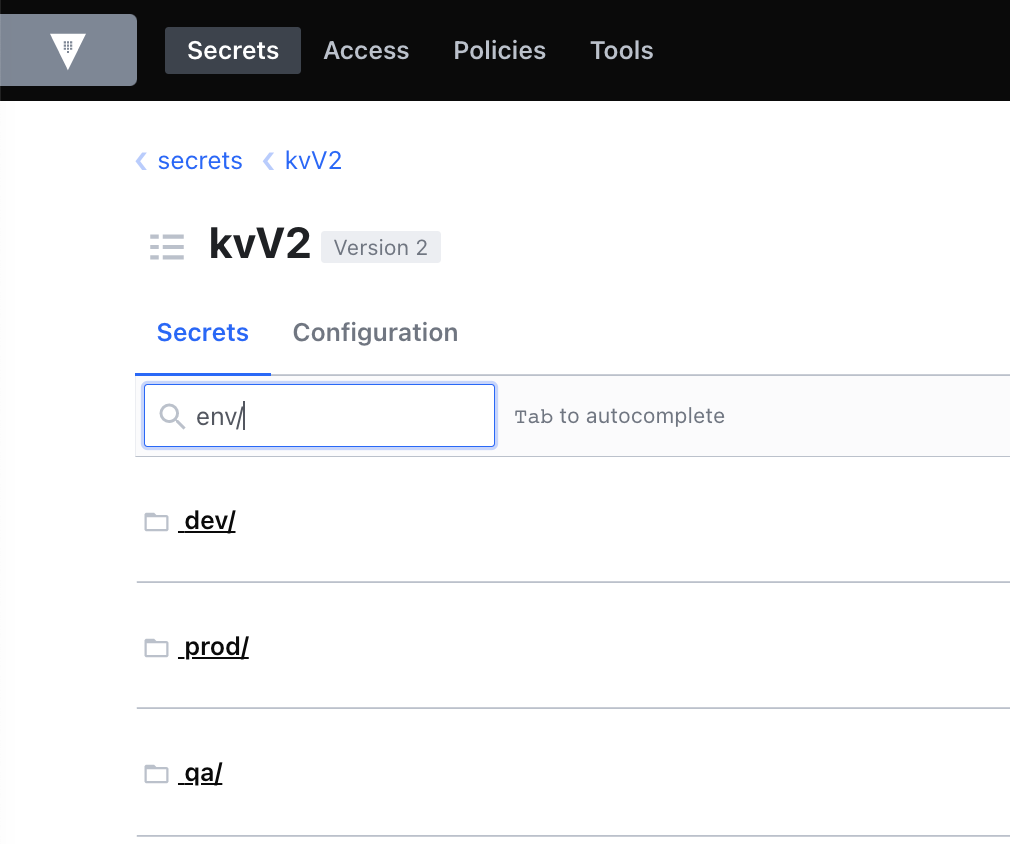
Screenshot from UI:-
How to write policy for specific users:
Policy for QA Users: qa.hcl
path "kvV2/metadata/env/qa/*"
{
capabilities = ["read","list"]
}
#to list and read all data of env path inside kv secret
path "kvV2/data/env/qa/*"
{
capabilities = ["read","list"]
}
# to list and read the secrets
path "kvV2/*"
{
capabilities = ["list"]
}
vault policy write qa qa.hcl
Policy for Dev Users: dev.hcl
path "kvV2/metadata/env/dev/*"
{
capabilities = ["read","list"]
}
#to list and read all data of env path inside kv secret
path "kvV2/data/env/dev/*"
{
capabilities = ["read","list"]
}
# to list and read the secrets
path "kvV2/*"
{
capabilities = ["list"]
}vault policy write dev dev.hcl
Policy for Prod Users: prod.hcl
path "kvV2/metadata/env/prod/*"
{
capabilities = ["read","list"]
}
#to list and read all data of env path inside kv secret
path "kvV2/data/env/prod/*"
{
capabilities = ["read","list"]
}
# to list and read the secrets
path "kvV2/*"
{
capabilities = ["list"]
}vault policy write prod prod.hcl
Verify the access for qa, dev & prod user to specific path inside the KV secret:
vault auth enable userpass
vault write auth/userpass/users/qaUser password=12345 policies=qa
vault write auth/userpass/users/devUser password=12345 policies=dev
vault write auth/userpass/users/prodUser password=12345 policies=prod
- Login to UI or CLI and access the path defined in assigned policy inside the KV to verify the access & also access the other paths which are not defined in policy(you must get un-authorise access error).
**NOTE:- For KV1 please remove the metadata & data from policy and keep policy like below:-
#to list and read all data of env path inside kv secret
path "kvV1/env/qa/*"
{
capabilities = ["read","list"]
}
# to list and read the secrets
path "kvV1/*"
{
capabilities = ["list"]
}
